In 2013, the Westmore Information, a modest newspaper serving the suburban neighborhood of Rye Brook, New York, ran a feature on the opening of a sluice gate at the Bowman Avenue Dam. Costing some $2 million, the new gate, then nearing completion, was created to lessen flooding downstream.
The event caught the eye of a variety of local politicians, who collected to shake palms at the formal unveiling. “I’ve been to lots of ribbon-cuttings,” county executive Rob Astorino was quoted as expressing. “This is my to start with sluice gate.”
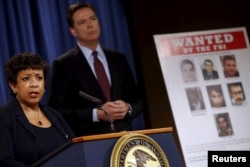
But locals seemingly were not the only ones with their eyes on the dam’s new sluice. According to an indictment handed down late final week by the U.S. Department of Justice, Hamid Firoozi, a nicely-identified hacker primarily based in Iran, acquired entry various instances in 2013 to the dam’s command devices. Had the sluice been completely operational and connected to those people units, Firoozi could have made critical destruction. The good thing is for Rye Brook, it was not.
Hack assaults probing crucial U.S. infrastructure are nothing new. What alarmed cybersecurity analysts in this circumstance, having said that, was Firoozi’s obvious use of an previous trick that laptop or computer nerds have quietly acknowledged about for a long time.
It really is termed “dorking” a search motor — as in “Google dorking” or “Bing dorking” — a tactic lengthy employed by cybersecurity industry experts who get the job done to close protection vulnerabilities.
Now, it appears, the hackers know about it as nicely.
Hiding in open see
“What some simply call dorking we actually simply call open up-supply network intelligence,” reported Srinivas Mukkamala, co-founder and CEO of the cyber-threat assessment agency RiskSense. “It all is dependent on what you check with Google to do.”
Mukkamala suggests that look for engines are frequently trolling the Online, searching to file and index every product, port and unique IP tackle linked to the Internet. Some of those issues are built to be public — a restaurant’s homepage, for instance — but lots of other people are meant to be private — say, the protection digicam in the restaurant’s kitchen. The dilemma, says Mukkamala, is that as well numerous folks don’t have an understanding of the change just before likely on the net.
“There’s the Web, which is anything at all that’s publicly addressable, and then there are intranets, which are meant to be only for inside networking,” he told VOA. “The look for engines really don’t care which is which they just index. So if your intranet is not configured adequately, that’s when you start observing information and facts leakage.”
Although a restaurant’s closed-circuit camera may perhaps not pose any real safety menace, a lot of other items acquiring related to the Internet do. These consist of tension and temperature sensors at power crops, SCADA programs that management refineries, and operational networks — or OTs — that keep important manufacturing crops functioning.
Whether engineers know it or not, many of these items are staying indexed by lookup engines, leaving them quietly hiding in open view. The trick of dorking, then, is to determine out just how to obtain all individuals property indexed online.
As it turns out, it’s definitely not that really hard.
An asymmetric threat
“The issue with dorking is you can generate personalized queries just to glance for that info [you want],” he stated. “You can have multiple nested search conditions, so you can go granular, enabling you to obtain not just just about every single asset, but each other asset which is linked to it. You can really dig deep if you want,” explained RiskSense’s Mukkamala.
Most significant search engines like Google present sophisticated look for functions: instructions like “filetype” to hunt for unique styles of information, “numrange” to locate particular digits, and “intitle,” which looks for correct site text. Additionally, various search parameters can be nested 1 in another, making a pretty fantastic digital net to scoop up data.
For case in point, rather of just entering “Brook Avenue Dam” into a search motor, a dorker could use the “inurl” perform to hunt for webcams on the web, or “filetype” to look for command and manage files and features. Like a scavenger hunt, dorking includes a specified quantity of luck and tolerance. But skillfully employed, it can greatly maximize the possibility of finding anything that really should not be general public.
Like most items on the internet, dorking can have good employs as very well as unfavorable. Cybersecurity gurus increasingly use this sort of open up-supply indexing to explore vulnerabilities and patch them in advance of hackers stumble on them.
Dorking is also absolutely nothing new. In 2002, Mukkamala suggests, he worked on a task checking out its possible hazards. Extra not too long ago, the FBI issued a community warning in 2014 about dorking, with tips about how network directors could defend their devices.
The problem, says Mukkamala, is that virtually something that can be related is becoming hooked up to the Internet, generally with out regard for its security, or the stability of the other objects it, in convert, is related to.
“All you will need is one particular vulnerability to compromise the system,” he advised VOA. “This is an uneven, popular menace. They [hackers] you should not need to have something else than a laptop and connectivity, and they can use the instruments that are there to begin launching assaults.
“I really don’t consider we have the information or means to defend towards this risk, and we are not ready.”
That, Mukkamala warns, suggests it really is much more very likely than not that we’ll see much more conditions like the hacker’s exploit of the Bowman Avenue Dam in the years to arrive. Sad to say, we could possibly not be as blessed the next time.